ROP绕过片段简单科普一下,你可以理解成一个可以关闭系统自身内存保护的一段机器指令,这段代码需要我们自己构造,这就涉及到在对端内存搜寻这样的指令,LyScript插件增强了指令片段的查找功能,但需要我们在LyScript插件基础上封装一些方法,实现起来也不难。
LScript项目地址:https://github.com/lyshark/LyScript
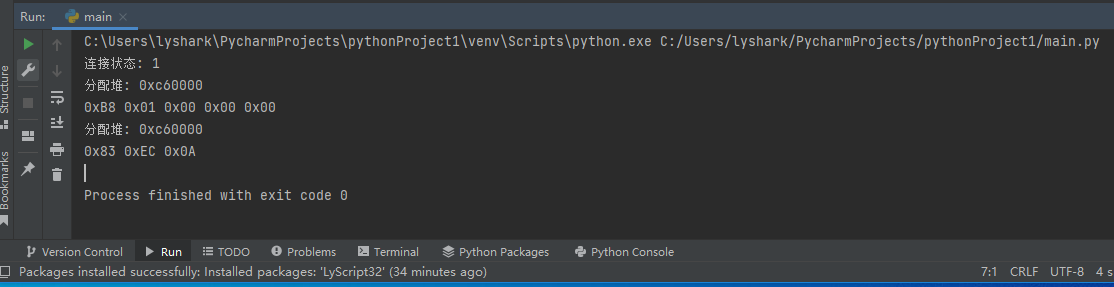
封装机器码获取功能: 首先封装一个方法,当用户传入指定汇编指令的时候,自动的将其转换成对应的机器码,这是为搜索ROP片段做铺垫的,代码很简单,首先dbg.create_alloc(1024)在进程内存中开辟堆空间,用于存放我们的机器码,然后调用dbg.assemble_write_memory(alloc_address,"sub esp,10")将一条汇编指令变成机器码写到对端内存,然后再op = dbg.read_memory_byte(alloc_address + index)依次将其读取出来即可。
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
|
from LyScript32 import MyDebug# 传入汇编指令,获取该指令的机器码def get_assembly_machine_code(dbg,asm): passif __name__ == "__main__": dbg = MyDebug() connect_flag = dbg.connect() print("连接状态: {}".format(connect_flag)) machine_code_list = [] # 开辟堆空间 alloc_address = dbg.create_alloc(1024) print("分配堆: {}".format(hex(alloc_address))) # 得到汇编机器码 machine_code = dbg.assemble_write_memory(alloc_address,"sub esp,10") if machine_code == False: dbg.delete_alloc(alloc_address) # 得到汇编指令长度 machine_code_size = dbg.assemble_code_size("sub esp,10") if machine_code == False: dbg.delete_alloc(alloc_address) # 读取机器码 for index in range(0,machine_code_size): op = dbg.read_memory_byte(alloc_address + index) machine_code_list.append(op) # 释放堆空间 dbg.delete_alloc(alloc_address) # 输出机器码 print(machine_code_list) dbg.close() |
我们继续封装如上方法,封装成一个可以直接使用的get_assembly_machine_code函数。
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
|
from LyScript32 import MyDebug# 传入汇编指令,获取该指令的机器码def get_assembly_machine_code(dbg,asm): machine_code_list = [] # 开辟堆空间 alloc_address = dbg.create_alloc(1024) print("分配堆: {}".format(hex(alloc_address))) # 得到汇编机器码 machine_code = dbg.assemble_write_memory(alloc_address,asm) if machine_code == False: dbg.delete_alloc(alloc_address) # 得到汇编指令长度 machine_code_size = dbg.assemble_code_size(asm) if machine_code == False: dbg.delete_alloc(alloc_address) # 读取机器码 for index in range(0,machine_code_size): op = dbg.read_memory_byte(alloc_address + index) machine_code_list.append(op) # 释放堆空间 dbg.delete_alloc(alloc_address) return machine_code_listif __name__ == "__main__": dbg = MyDebug() connect_flag = dbg.connect() print("连接状态: {}".format(connect_flag)) # 转换第一对 opcode = get_assembly_machine_code(dbg,"mov eax,1") for index in opcode: print("0x{:02X} ".format(index),end="") print() # 转换第二对 opcode = get_assembly_machine_code(dbg,"sub esp,10") for index in opcode: print("0x{:02X} ".format(index),end="") print() dbg.close() |
执行后即可得到结果:
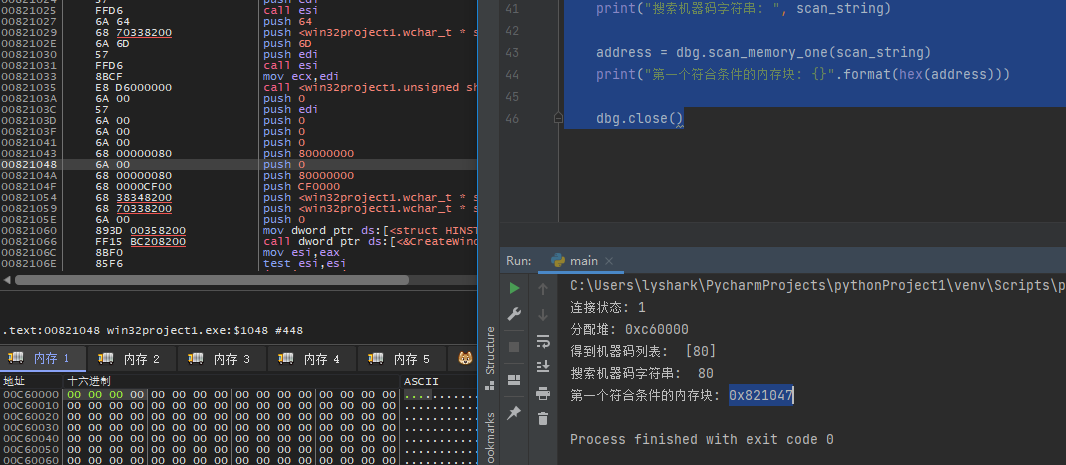
扫描符合条件的内存: 通过使用上方封装的get_assembly_machine_code()并配合scan_memory_one(scan_string)函数,在对端内存搜索是否存在符合条件的指令。
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
|
from LyScript32 import MyDebug# 传入汇编指令,获取该指令的机器码def get_assembly_machine_code(dbg,asm): machine_code_list = [] # 开辟堆空间 alloc_address = dbg.create_alloc(1024) print("分配堆: {}".format(hex(alloc_address))) # 得到汇编机器码 machine_code = dbg.assemble_write_memory(alloc_address,asm) if machine_code == False: dbg.delete_alloc(alloc_address) # 得到汇编指令长度 machine_code_size = dbg.assemble_code_size(asm) if machine_code == False: dbg.delete_alloc(alloc_address) # 读取机器码 for index in range(0,machine_code_size): op = dbg.read_memory_byte(alloc_address + index) machine_code_list.append(op) # 释放堆空间 dbg.delete_alloc(alloc_address) return machine_code_listif __name__ == "__main__": dbg = MyDebug() connect_flag = dbg.connect() print("连接状态: {}".format(connect_flag)) # 转换成列表 opcode = get_assembly_machine_code(dbg,"push eax") print("得到机器码列表: ",opcode) # 列表转换成字符串 scan_string = " ".join([str(_) for _ in opcode]) print("搜索机器码字符串: ", scan_string) address = dbg.scan_memory_one(scan_string) print("第一个符合条件的内存块: {}".format(hex(address))) dbg.close() |
扫描结果如下:
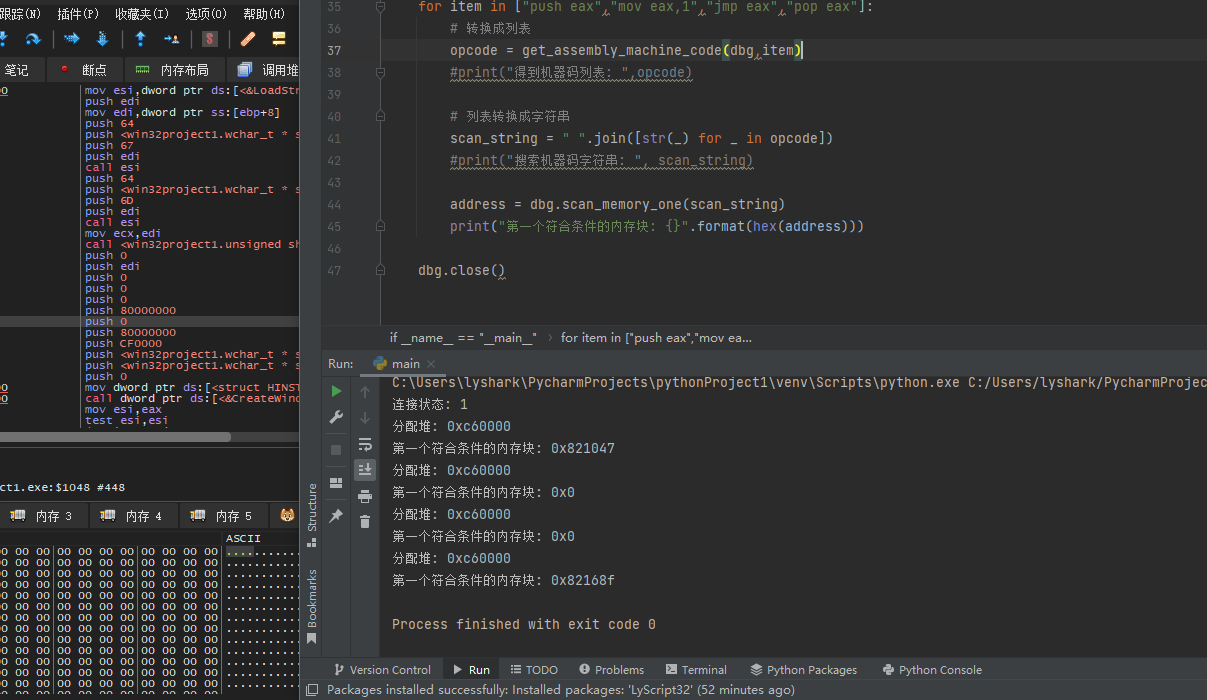
将我们需要搜索的ROP指令集片段放到数组内直接搜索,即可直接返回ROP内存地址。
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
|
from LyScript32 import MyDebug# 传入汇编指令,获取该指令的机器码def get_assembly_machine_code(dbg,asm): machine_code_list = [] # 开辟堆空间 alloc_address = dbg.create_alloc(1024) print("分配堆: {}".format(hex(alloc_address))) # 得到汇编机器码 machine_code = dbg.assemble_write_memory(alloc_address,asm) if machine_code == False: dbg.delete_alloc(alloc_address) # 得到汇编指令长度 machine_code_size = dbg.assemble_code_size(asm) if machine_code == False: dbg.delete_alloc(alloc_address) # 读取机器码 for index in range(0,machine_code_size): op = dbg.read_memory_byte(alloc_address + index) machine_code_list.append(op) # 释放堆空间 dbg.delete_alloc(alloc_address) return machine_code_listif __name__ == "__main__": dbg = MyDebug() connect_flag = dbg.connect() print("连接状态: {}".format(connect_flag)) for item in ["push eax","mov eax,1","jmp eax","pop eax"]: # 转换成列表 opcode = get_assembly_machine_code(dbg,item) #print("得到机器码列表: ",opcode) # 列表转换成字符串 scan_string = " ".join([str(_) for _ in opcode]) #print("搜索机器码字符串: ", scan_string) address = dbg.scan_memory_one(scan_string) print("第一个符合条件的内存块: {}".format(hex(address))) dbg.close() |
检索效果如下:
到此这篇关于LyScript寻找ROP漏洞指令片段的方法详解的文章就介绍到这了,更多相关LyScript ROP漏洞指令片段内容请搜索服务器之家以前的文章或继续浏览下面的相关文章希望大家以后多多支持服务器之家!
原文链接:https://www.cnblogs.com/LyShark/p/16522301.html