lnmp是什么 : linux+nginx+mysql+(php-fpm,php-mysql)
即在linux操作系统上nginx+mysql+php的网站服务架构。
centos 6中为mysql,centos 7中为mariadb
作用是什么 : 提供web服务,并可以解析php类的应用程序;
下面我就利用lnmp架构部署phpmyadmin:
前提:这次操作均在172.16.75.1主机上进行;
1. 为web服务器配置一个域名:www.sss.com
在物理机的c盘下的windows/system32/drivers/etc/etc/hosts文件中添加一条记录:
172.16.75.1 www.sss.com
2. 在172.16.75.1主机上部署lnmp架构:
|
1
|
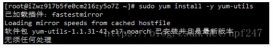
[root@master ~]# yum install nginx mariadb php-fpm php-mysql |
在这估计大家会提出疑问,php-fpm,php-mysql的作用是什么呢?
因为nginx只是提供web服务,不能解析php应用,而php-fpm可以
而php-mysql用来连接php应用和mariadb的;
3. 配置:
|
1
|
[root@master ~]# vim /etc/nginx/nginx.conf |
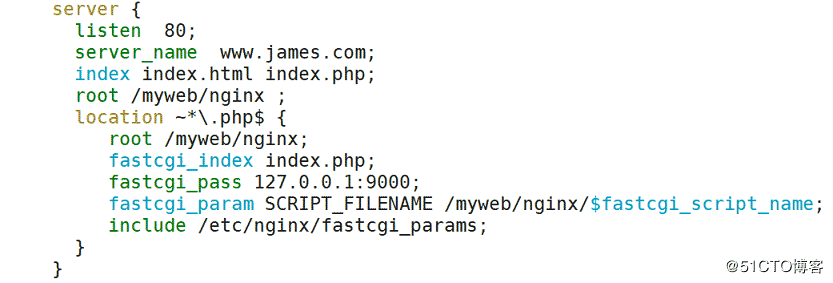
|
1
2
3
|
[root@master ]# nginx -tnginx: the configuration file /etc/nginx/nginx.conf syntax is oknginx: configuration file /etc/nginx/nginx.conf test is successfu |
测试nginx配置无错,开启服务:
|
1
|
[root@master ~]# systemctl start nginx |
开启php-fpm服务:
|
1
|
[root@master ~]# systemctl start php-fpm |
创建一个目录用于存放资源,在nginx.conf中已经定义:
|
1
|
[root@master ~]# mkdir -pv /myweb/nginx/ |
我事先已将wordpress和phpmyadmin的包放到该目录下:
首先部署phpmyadmin(用来管理数据库)应用
解压:
|
1
2
3
|
[root@master ~]# cd /myweb/nginx/[root@master nginx]# tar -xf phpmyadmin-3.5.4-all-languages.tar.gz [root@master nginx]# mv phpmyadmin-3.5.4-all-languages pma |
在/var/lib/php下创建目录session:
属主为root,属组为apache,权限为770;
|
1
2
3
4
|
[root@master ~]# cd /var/lib/php[root@master php]# mkdir session[root@master php]# chown root:apache session/[root@master php]# chmod 770 session/ |
给管理员配置一个数据库的管理密码:
|
1
2
|
[root@master ~]# mysqladmin -p'' password '111111'enter password: |
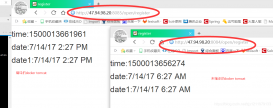
完成后,在web端进行访问测试:

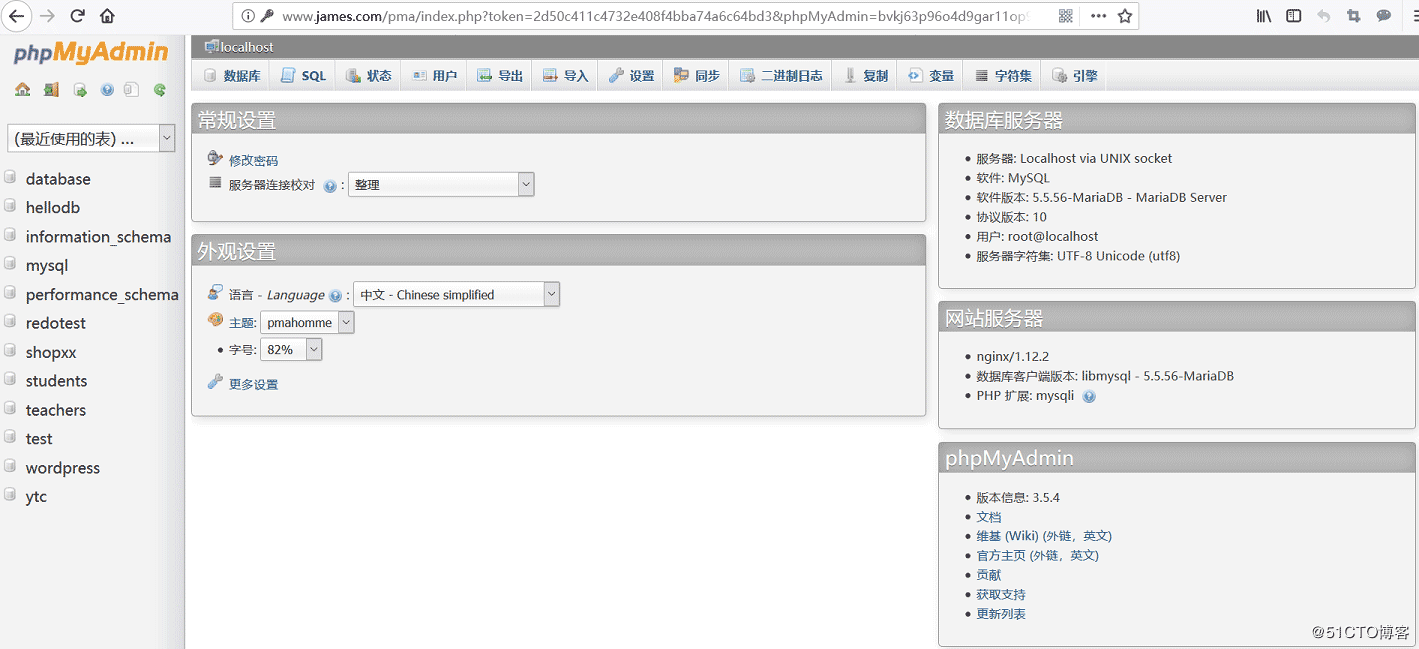
这样phpmyadmin部署完成。
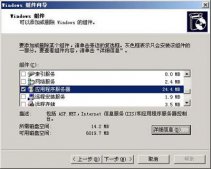
接下来为phpmyadmin提供https服务:
|
1
2
3
4
5
|
[root@master ~]# cd /etc/pki/ca/[root@master ca]# (umask 077;openssl genrsa -out private/cakey.pem 2048)[root@master ca]# openssl req -new -x509 -key private/cakey.pem -out cacert.pem -days 3653[root@master ca]# touch index.txt[root@master ca]# echo 01 > serial |
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
|
[root@master ssl]# (umask 077;openssl genrsa -out nginx.key 2048)[root@master ssl]# openssl req -new -key nginx.key -out nginx.csr -days 3653[root@master ssl]# openssl ca -in nginx.csr -out /etc/pki/ca/certs/nginx.crt -days 3653using configuration from /etc/pki/tls/openssl.cnfcheck that the request matches the signaturesignature okcertificate details: serial number: 1 (0x1) validity not before: nov 12 14:15:57 2018 gmt not after : nov 12 14:15:57 2028 gmt subject: countryname = cn stateorprovincename = hebei organizationname = james organizationalunitname = james.edu commonname = www.james.com x509v3 extensions: x509v3 basic constraints: ca:false netscape comment: openssl generated certificate x509v3 subject key identifier: 5a:68:d6:47:29:da:a5:29:98:09:0d:82:02:2d:b1:5d:61:8a:26:ec x509v3 authority key identifier: keyid:32:b2:8d:ac:68:57:fc:bf:8b:f2:ca:68:8b:45:93:d4:7f:a2:25:f3 [root@master ssl]# scp /etc/pki/ca/certs/nginx.crt ./[root@master ssl]# rm -f nginx.csr |
修改nginx配置文件:
|
1
|
[root@master ssl]# vim /etc/nginx/nginx.conf |
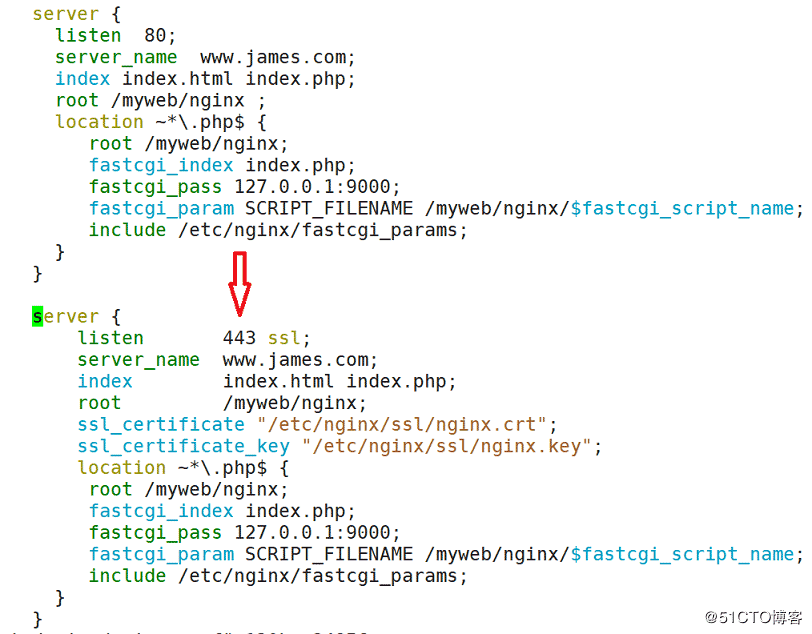
检测无误后重启nginx服务:
|
1
2
|
[root@master ssl]# nginx -t[root@master ssl]# nginx -s reload |
web端测试:
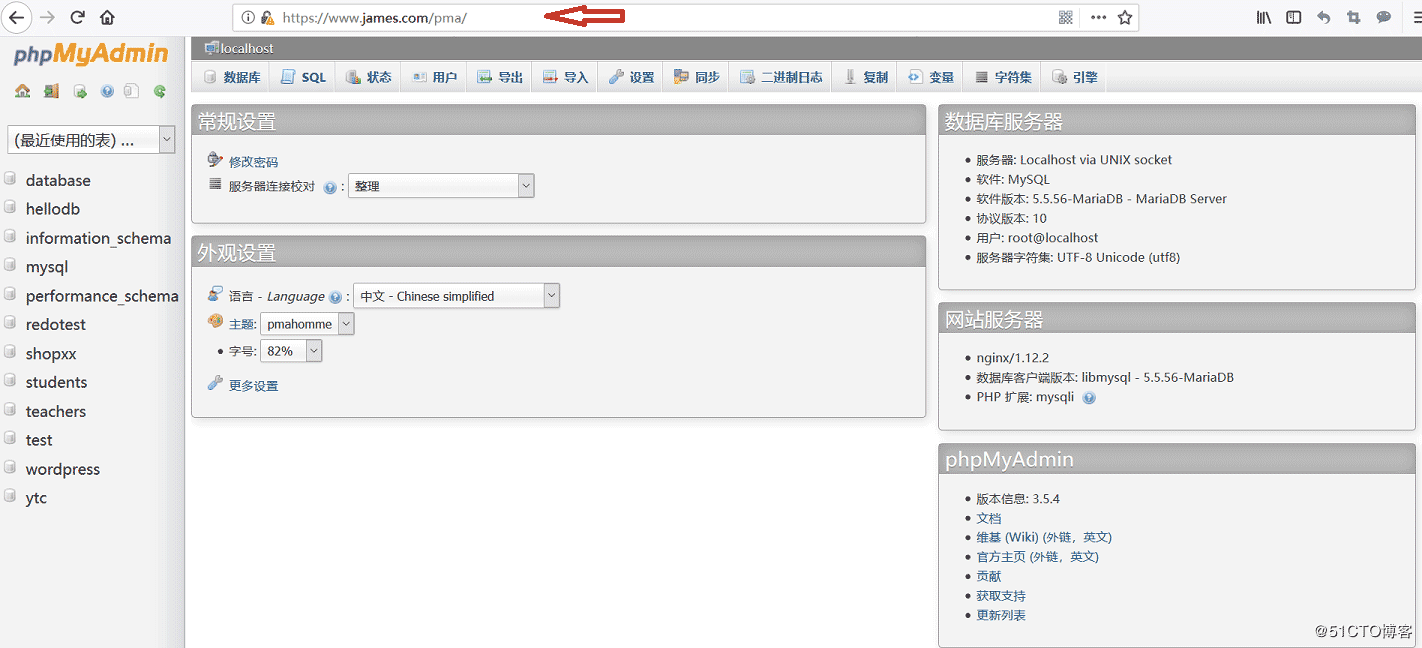
https服务实现。
原文链接:http://blog.51cto.com/yuantianchi/2316103